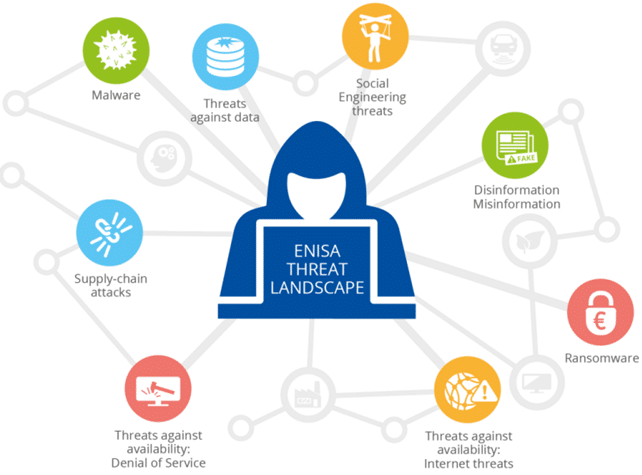
Image from the ENISA Threat Landscape Report 2022
Author: Efi Kafali / CERTH
In the domain of cybersecurity, KINAITICS takes a technical leap forward with its focused approach to AI threat mitigation. This article discusses the technical approach outlined in D3.1, touching on the methodology that supported the creation of the KINAITICS Threat Matrix. Specifically designed to navigate the dynamic landscape of AI-enabled threats, the matrix is tailored to the unique requirements of KINAITICS use cases. Our analysis revolves around two key threat taxonomies—the MITRE ATLAS framework and the ENISA Threat Landscape (ETL) Report—specifically addressing AI-enabled threats. Additionally, we incorporate insights from state-of-the-art academic research in cyber/physical attacks, elevating the technical foundation of the KINAITICS approach.
While the MITRE ATLAS framework offers a wealth of cyber-attack tactics, our detailed examination highlights the necessity for customization specifically designed for the unique use cases within KINAITICS. The limitations in tactic specificity and considerations of human factors in cyber-attacks drive us to refine our framework further. Simultaneously, the ENISA ETL Report provides a clear understanding of the evolving threat landscape but demands continuous technical updates to tackle emerging threats. Its broad coverage may not precisely align with KINAITICS’ AI-centric focus.
Adopting a data-driven, technically sound approach, we advocate for the creation of a tailored Threat Matrix as an essential component for the success of the KINAITICS project. By homogenizing insights from the MITRE ATLAS framework, the ENISA ETL Report, and cutting-edge research in AI-enabled attacks, we devise a customized Threat Matrix that distinctly addresses AI-related threats unique to KINAITICS.
This technical precision enables us to identify and mitigate relevant threats and vulnerabilities proactively. Our analysis of each use case’s technical context, critical assets, and attack surface empowers us to identify potential threats exploiting AI-driven vulnerabilities, mapping them to the KINAITICS Threat Matrix. D3.1 concludes by outlining preliminary technical defense strategies and countermeasures based on our findings.
The resulting tailored Threat Matrix serves as the robust technical foundation for the KINAITICS project’s cybersecurity defense strategy.
Moving forward, the KINAITICS project is committed to fostering technical collaboration and knowledge sharing among consortium partners, facilitating advancements in cybersecurity technology and ensuring a future for AI-enabled technologies.

